FiA 64: Advanced Forensic Image Authentication for Digital Evidence Integrity
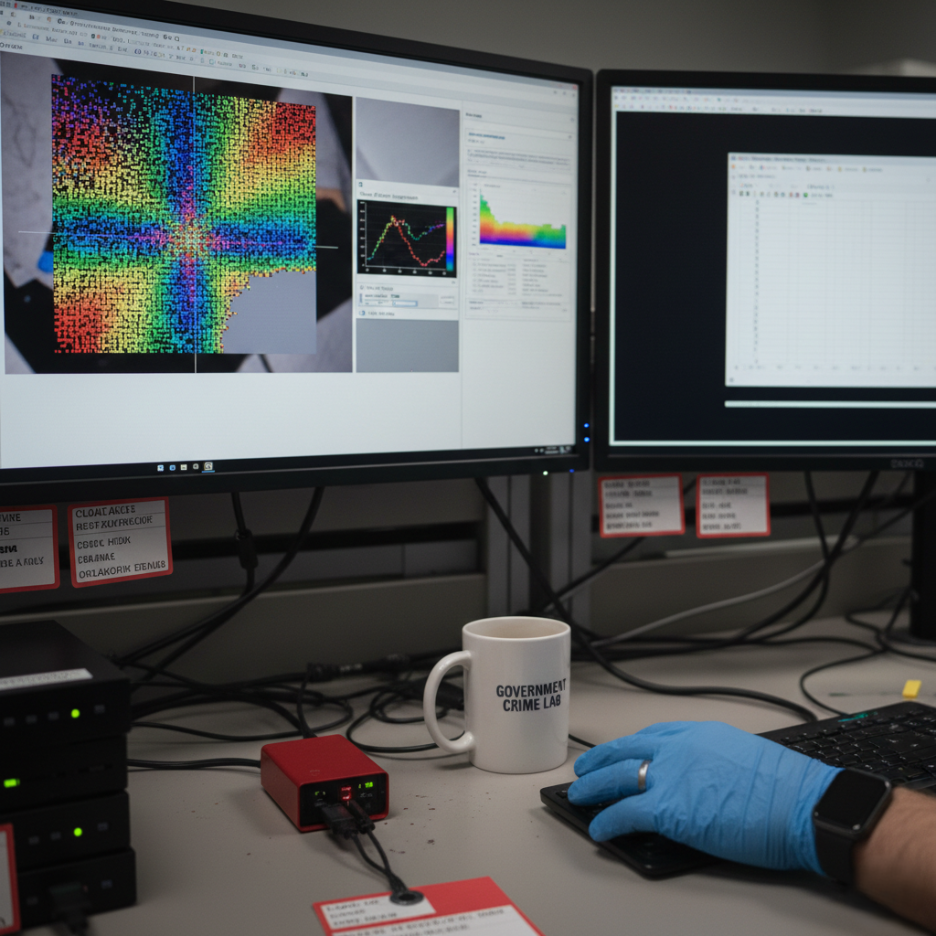
Modern investigations depend on digital imagery, which creates challenges for evidence reliability because of its easy manipulation. Cognitech developed FiA 64 to provide a solution which uses scientific methods for forensic image authentication. The platform enables law enforcement agencies and forensic laboratories and governmental bodies to examine digital image files through its system which detects digital file alteration. The system examines three types of data which include visual data and digital compression information and metadata and sensor-generated patterns to produce results which testing organizations can use to reproduce results.
The 64-bit system of FiA 64 enables it to handle high-resolution files through its complete analytical processing system. Objective forensic image authentication has become essential for the current system because technical challenges and legal requirements must be satisfied.
Core Analytical Capabilities
The system of FiA 64 includes more than thirty authentication routines which assess digital evidence from different technical angles. The system uses five distinct technical methods which include EXIF metadata extraction and DCT coefficient evaluation and quantization table inspection and adaptive error level analysis and Photo Response Non-Uniformity comparisons. The system creates results which include correlation maps and probability distributions and numerical metrics that users can use to build structured reports.
Laboratories can use batch processing to create standardized forensic image authentication methods which they can apply to their entire collection of evidence files. The fast batch presets system enables examiners to execute testing sequences which create less interpretive differences while making their operations run more efficiently. FiA 64 produces analytical results which users can export to make all evaluation processes accessible for review and assessment.
Scientific Reporting and Transparency
The primary element which defines FiA 64 functions as its documentation framework. The system enables users to export analytical maps and statistical summaries for their use in technical reports. The three elements provide measurable results which enable users to obtain concrete findings instead of relying on subjective impressions.
The structured approach to forensic image authentication establishes a foundation for authentication through measurable evidence. Reproducibility and transparency represent the essential elements which judicial systems require to challenge digital evidentiary materials.
Integration Within Investigative Workflows
FiA 64 functions as an authentication system while being part of larger forensic investigation networks. Investigators need visual clarification to understand structural tests according to certain investigation cases. Agencies depend on approved image enhancement software to process their requirements when they need to boost specific image content under documented conditions.
Forensic image authentication depends on the specific processes which separate preprocessing work from all image authentication tasks. Image enhancement software adjustments must receive complete documentation to make sure all evidence stays intact. The choice of validated image enhancement software guarantees that all image clarification procedures will not create deceptive artifacts before the authentication examination starts.
Clear policies governing image enhancement software usage reduce procedural ambiguity. Laboratories should document parameter settings and maintain preserved originals before proceeding with authentication routines.
Legal Strength and Repeatability
The system of FiA 64 produces results which multiple users can replicate while establishing legal defensibility. The application of identical parameter sets throughout all cases enables examiners to sustain their forensic image authentication methods. The system allows independent reviewers to check analytical steps through its exportable logs and structured outputs.
The use of approved image enhancement software requires documentation which includes all parameters for visual clarification to establish credibility. The authentication process needs to stay separate from image enhancement software procedures to maintain the credibility of all findings.
Digital forensic results in courts need to have concrete evidence which backs them up. The system of FiA 64 requires users to use statistical assessment methods and structured document methods instead of using personal interpretation.
Deployment and training considerations
The process of adopting forensic-grade software needs organizations to develop a comprehensive plan. Agencies need to evaluate their requirements for data management and GPU/CPU processing power and they need to establish secure storage methods which will protect their raw and processed data and they need to determine retention guidelines which will comply with both their legal requirements and their internal standards. Organizations can use Cognitech’s system which supports both on-premises and cloud-based operations to select their preferred architecture for protecting security and managing costs.
Training holds the same level of significance as other elements do. Vendors need to provide scenario-based training for their analysts to develop skills in using tools and understanding courtroom procedures for creating documentation and providing testimony. The investigative team achieves maximum investigative value through their extensive training on forensics software while they maintain reduced legal risk exposure.
The current systems create a seamless process for connecting with case management systems and evidence databases through their modern API capabilities and standardized export procedures. The video exhibits and annotations and measurement reports can securely exchange metadata information through Cognitech which enables direct linking to case file documents. The system reduces unnecessary duplication by maintaining case documentation while it accelerates the transfer process between investigators and analysts and prosecutors. The system streamlines team collaboration processes for response teams who need to work together.
Get Court-Ready Image Authentication Software Now
Conclusion
The system of FiA 64 enables scientific validation of digital imagery through its organized testing process, which produces measurable results and documented workflows. The authentication analysis process needs to stay separate from controlled preprocessing steps, which laboratories should execute to maintain evidentiary integrity and transparency. The system of FiA 64 improves investigative confidence through its digital evidence protection, which maintains legal standing in judicial situations when users implement proper training and governance policies and tool management, according to the system requirements.
Talk with experts for Forensic video Processing Software and Forensic Image Processing Software solutions. Contact Cognitech! We hope you enjoyed this Blog! Stay tuned, and don’t miss the coming blogs. You can follow us on Twitter, Facebook, Instagram, Linkedin, or Youtube: we post Community Blogs regularly so you won’t miss any!
FAQs
1. What is forensic image authentication software used for?
Forensic image authentication software verifies digital image integrity by detecting manipulation, analyzing metadata, and identifying inconsistencies to ensure images remain admissible and defensible in legal investigations.
2. How does image enhancement software support forensic analysis?
Image enhancement software improves clarity, adjusts contrast, and reveals hidden details without altering original evidence, supporting investigators during authentication and technical examination processes.
3. Is forensic image authentication admissible in court?
When properly documented and validated, forensic image authentication methods can support courtroom proceedings by providing traceable analysis, structured reports, and scientifically defensible verification results.
4. Who should use forensic image authentication tools?
Law enforcement agencies, digital forensic analysts, legal professionals, cybersecurity teams, and investigative journalists rely on forensic image authentication tools for secure digital evidence verification.
