Ensuring Image Integrity: A Practical Guide to Modern Evidence Validation
Digital images have become essential components of investigations and courtroom proceedings and media verification processes. When analysts need to establish image provenance, they use systematic workflows together with specific tools to identify original images and detect altered content. Forensic image authentication relies on disciplined examination practices and the appropriate technology framework to identify hidden evidence of tampering.
What a rigorous authentication workflow looks like
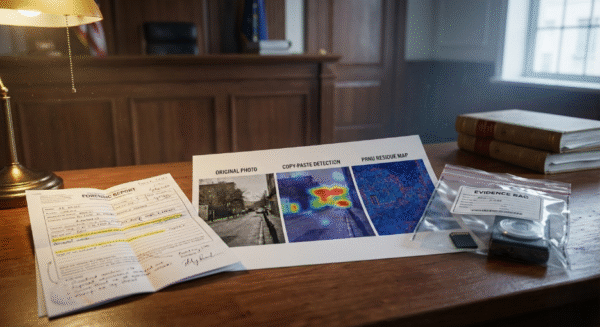
The trustworthy procedure begins with original file preservation together with metadata acquisition before it proceeds to multiple examination stages which evaluate the file’s composition as well as its compression artifacts and sensor signatures and its regional pattern discrepancies. Image authentication software enables experienced practitioners to conduct structured tests which involve EXIF extraction and DCT and quantization analysis together with error-level algorithms and correlation/PRNU checks to establish a reproducible evidentiary chain. The testing process identifies specific indicators of double JPEG compression and copy/paste cloning and edits which disrupt the anticipated sensor interpolation pattern.
The current analytical toolkits which vendors sell include multiple analysis methods that enable examiners to conduct automated scanning and manual inspection based on actual requirements. The commercial solution offers more than thirty authentication functions which include specialized mapping tools such as DCT map CL map CFA map Differential Map and PRNU residue to assist investigators in detecting and measuring irregularities through visual data instead of personal judgment. The features transform doubtful evidence into measurable elements which can be formally documented in an official report.
Methods that routinely find manipulations
The most effective test requires multiple independent methods to establish evidence through cross-method confirmation. Compression-level analysis together with JPEG DCT mapping techniques reveal unauthorized alterations to recompression patterns. Error Level Analysis and its adaptive/smart variants designate specific regions which have distinct recompression patterns that differ from the complete image as potential editing locations. PRNU-based methods analyze the sensor fingerprint of an unknown image to identify suspected copy/paste or cross-camera authentic prints.
Forensic image authentication becomes repeatable and credible because of established digital imaging pipeline statistical and physical characteristics. Batching and automated folder processing are essential elements which enhance operational performance. Investigators can utilize file-batching workflows to process their entire case file when they need to analyze multiple images by running analytical functions across all files in the selected group. The research-based authentication software for image authentication becomes a standard investigative tool because it decreases manual work while preserving complete analytical process traceability.
Reporting, training, and courtroom readiness
The report phase which receives inadequate attention represents the final stage of authentication work. The vendors direct their products to law enforcement agencies by offering training packages which help examiners gain product knowledge about automated analysis capabilities and limitations. Institutional training functions as the key element which prevents people from misinterpreting certain results. Forensic image authentication tools enable credible testimony by connecting visual evidence to scientifically established methods.
Protect the Authenticity of Image Evidence
Analyze and verify digital images with advanced forensic authentication tools.
Learn MoreConclusion
The investigative field requires both rigorous investigative methods together with advanced investigative tools because image manipulation tools have become highly accessible and realistic. Image authentication software selection combined with proper usage creates a path which leads to evidence-based outcomes for determining image trustworthiness. Forensic image authentication methods gain strength through precise image handling and cross-validation together with open reporting which establishes visuals as trustworthy evidence.
Talk with experts for Forensic video Processing Software and Forensic Image Processing Software solutions. Contact Cognitech! We hope you enjoyed this Blog! Stay tuned, and don’t miss the coming blogs. You can follow us on Twitter, Facebook, Instagram, Linkedin, or Youtube: we post Community Blogs regularly so you won’t miss any!
FAQs
- What is forensic image authentication?
It is a process used to verify whether a digital image is original or manipulated using scientific and technical analysis methods. - What does image authentication software do?
It analyzes metadata, compression patterns, and pixel-level inconsistencies to detect edits, cloning, or tampering in images. - Is forensic image authentication reliable for investigations?
Yes, when multiple methods are used together, it provides reliable evidence for law enforcement and legal professionals. - Can all edited images be detected?
No, but combining several forensic techniquesgreatly improves the chances of identifying image manipulation.
